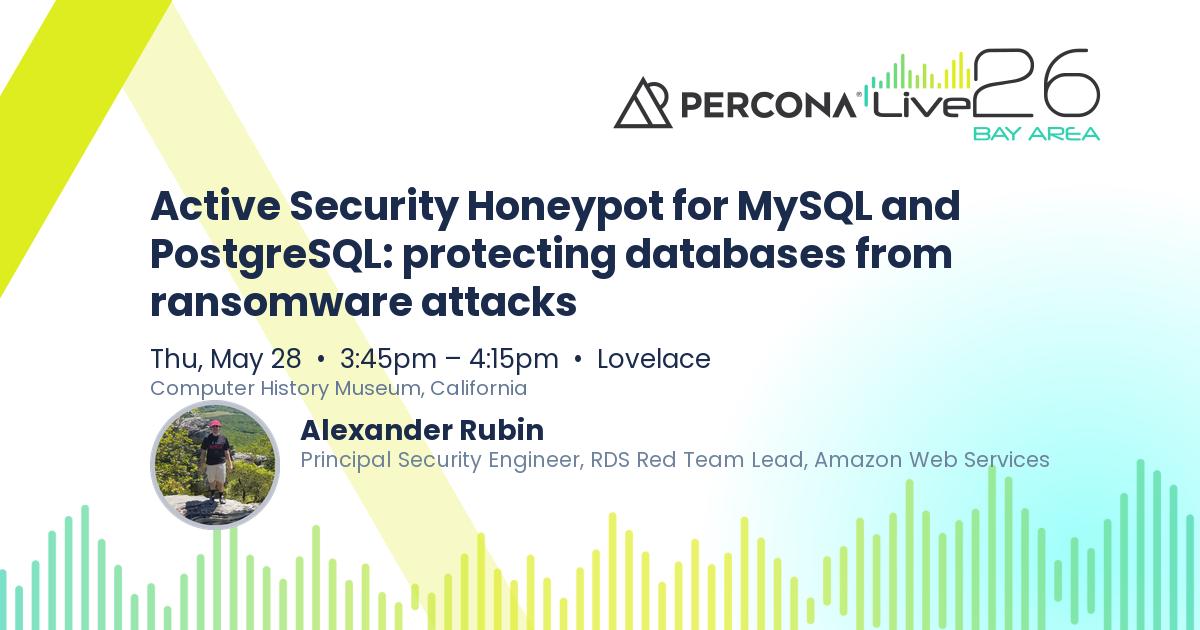
Active Security Honeypot for MySQL and PostgreSQL: protecting databases from ransomware attacks

Summary
Meet Active Security Honeypot for MySQL and PostgreSQL. In this presentation we will demonstrate the Active Security Honeypot (aka Atomic Honeypot that can drop shells) in action, present newly found security vulnerabilities in MySQL and demo the POC of MySQL plugin that can protect from ransomware.
Details
Database-centric ransomware activity can be traced back to early 2017, when large automated campaigns exploited internet-exposed, unauthenticated database servers (notably MongoDB) by scanning for open instances, copying or wiping their contents, and leaving ransom demands in exchange for return of the data. Security reporting at the time showed that tens of thousands of MongoDB installations were compromised, affecting over 22,000 database systems due to misconfiguration, with attackers demanding cryptocurrency payments (1)
Since then researchers have documented database ransom attacks as a distinct class of threat in which attackers identify accessible database servers (e.g.MySQL, PostgreSQL as well as MongoDB, Elasticsearch), log in using weak or absent authentication, remove data, insert ransom notes, and demand payment for return of the deleted database contents. A systematic study of these attacks observed over 60K compromised database servers over three years and identified campaigns that continued to infect thousands of systems yearly, with a 60 % increase in newly infected servers in March 2024 compared with a year earlier (2)
In 2023 I started MySQL security research focusing on a novel scenario where a compromised, rogue database server can attack a user connecting to it. I have discovered a new attack vector that allows a malicious MySQL server to attack MySQL client libraries, which can lead to remote code execution (RCE) on the client machine. We presented this research at the HITBSecConf2023 Amsterdam conference in Apr 2023 (3)
From there, in 2024, I have created a high interaction MySQL honeypot designed to attract and analyze attackers targeting MySQL databases by exploiting a vulnerability that allows a rogue server to attack connecting clients. Our goals were to capture detailed information about attacker tools, techniques, and procedures (TTPs) and to demonstrate that client-side security is crucial when connecting to untrusted databases. The honeypot allowed us to collect additional information about the ransomware attacks including full fingerprints/queries as well as malicious source code used by attackers. We presented that at Defcon US 2024 (4) and BlackHat Europe Arsenal 2025 (5). In 2025 we have opensourced the honeypot tool by the name of Active Security HoneyPot for MySQL (6) and created a prototype of PostgreSQL active security honeypot.
The information we collected with the database honeypots allowed us to design a solution to protect customers from ransomware attacks. We have decided to use a database plugin (rather than changing source code or using proxy) for better flexibility and ease of use/adoption. The plugin architecture allows the use of the existing query parsing mechanism (audit log) available in both MySQL and PostgreSQL. The new ransomware protection plugin can block destructive operations in real time, protecting the customers from data loss.
Download imageSpeaker

Alexander is a Principal Security at Amazon Web Services (AWS), leading RDS Red Team. Alexander was working as MySQL principal consultant/architect for over 15 years, started with MySQL AB in 2006 (company behind MySQL …